When it comes to Information Security, even the tiniest looking program could be a time bomb waiting to receive commands from an attacker to initiate a deadly attack on your system. The program could turn out to be a simple backdoor that initiates a connection to the attackers network waiting to receive commands and also to be able to steal information.
In one sentence, a backdoor is a piece of software that gives someone remote access to a computer, usually without the right permission when installed on the computer. The main purpose of a backdoor is to send and receive data, mostly commands, through a network system to and fro.
The attacker installs an innocent-seeming malicious program that could be a simple software or game. Once the user opens the program, the backdoor code hidden in the program could initiate a connection remotely to the attackers network and run any given commands.
It could also daemonize itself and run in the background process, so it doesn’t need you to open the program anymore to initiate a connection.
No matter how security conscious the user is, if someone can trick the user in opening the wrong program, they get to compromise and gain access to the user system remotely.
In this article, we’ll be building a simple backdoor program in Python and show how we can use it to exploit the user system.
Note: This is for educational purposes only, do not use against any person for illegal operations.
Getting Started
To get started, you need to have Python installed and running on your computer. Python is a good choice in this project as it is a high-level powerful programming language, and yes, it is easy and fast to implement as well as supported on all operating systems cross platforms.
If you don’t have Python installed, you can read this article on how to install and set it up on your system.
When building a backdoor, there are two components needed:
- Client: These are the components that will be installed on the victim computer, initiates a connection to the attackers network, accepts commands and sends data to and fro.
- Server: This is the component that will be installed on the attacker system acting as the entry point listening to the client connection, accepting the connection if it’s from the victim, sending commands and receiving data.
To make this work, we’ll be using the Socket module that comes built-in Python. The socket module is used to send data/messages to and fro over a network. In this case, the server will be sending commands (messages), the client receives a message (commands), sends a reply (data) and vice versa.
So we are going to be building two components: client.py and server.py.
Let’s see how to build the first component which is the Client component.
Build the Client Component
As explained earlier, the client component is responsible for initiating the connection, then waiting for commands from the attacker’s network, running the command and sending back a reply usually output of the command run.
Open the client.py:
Looking at the above code:
- We imported the modules we’ll be using – socket module (initiating our network connection) and subprocess (for running commands in shell)
- Declared the attackers (our) remote REMOTE_HOST and REMOTE_PORT. You should update the REMOTE_HOST with your IP or localhost – 127.0.0.1. You can get your IP here.
- Created the socket connection for client and connected it to our REMOTE server
- Then we added a while loop, that keeps listening and waiting for messages or commands
- We extracted the message from .recv(1024), decoded it to a string and passed it to the subprocess program responsible for running the command.
- After running the command, we check for both output and error, then send both along over the network.
To run this:
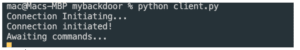
Voila! Our client component is ready.
Building the Server Component
The server component is responsible for listening for any incoming connection from the client’s component, accepting the connection, sending messages (commands) and receiving data.
Open the server.py:
Looking at the above code:
- We imported the socket module (for listening and accepting network connection)
- Declared our HOST and PORT. You should update the HOST with your IP or localhost – 127.0.0.1. You can get your IP here.
- Created the socket connection, listening to incoming connection and accepting, if any (when the user runs the program).
- We created a while loop to maintain connection between the client and server components.
- From here we can then ask the attacker to enter a command, send the command and get a response sent by the client component.
To run this:
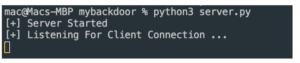
Voila! Our server component is also ready.
Testing Our Backdoor Program
Once you have successfully created the two components, we now have a simple backdoor software written with Python.
To test this, you will need to run the two components simultaneously and connected to the same HOST and PORT.
Open two terminals or command line and then run each command on each terminal.
Server: python server.py
Client: python client.py
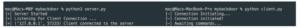
If you see outputs like the one in the image above, then both the server and client are connected and waiting to send and receive messages.
The server is ready to send commands while the client is ready to receive commands, run it and send back its output.
Now let’s enter this command in the server terminal: echo Hello World:
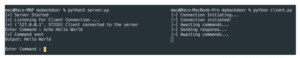
You should see something like the above image. We sent the command echo Hello World which means it should print out Hello World in the terminal. The client receives this command, runs it and sends back a response that is the output of the command.
Let’s try another like: ls -a ~, cat ~/.aws/config

Whoops! You can literally steal the user’s AWS access_key and access_id without their knowledge. Not only that, you can also run dangerous and do all sorts of things with this simple backdoor program.
With this, we can conclude that we have compromised the user computer and are able to gain access to the user computer and steal data.
Protecting Yourself Against Backdoor Attacks
These types of programs are very hard to detect and protect against as they are hidden away from plain sight and control.
There have been a lot of news on how people have been discovering backdoors in different programs for user programs, open source projects and even large software organizations. Backdoors are able to be injected in any kind of programs regardless of the operating system used on.
Backdoors are heavily built on the networking system to initiate remote connection to the attacker as we have seen in the program we built earlier. Most operating systems have firewalls monitoring any unusual and suspicious traffic to and fro. However, sometimes firewalls fail to detect the backdoor due to how backdoors send their network traffic just like how browsers or other apps would connect to the internet.
To prevent this, you can create policies in your firewall and choose which programs you would like to have access to the internet and any other traffic is blocked. For companies, they can create policies and selectively decide which device and application has access to the internet.
This reduces the chance of having a software you barely use serving as a backdoor gateway to steal your data.
Also the best way to protect yourself is to not trust any software, as most software is injected with backdoor code without the knowledge of the developers. Some of these applications are injected by some of the packages and dependencies used in building the application.
These dependencies could be open source and already have a backdoor in it. So any software using the dependencies in their software already has a backdoor in their program without them knowing.
So have zero-trust for any software.
Conclusion
In this article, we have explained what a backdoor is, how innocent-looking and dangerous it could be and how to build one. These kinds of programs are a big threat because it’s hard to detect them as they’re hidden in a simple program and can look like normal software. Most backdoor programs are bundled as .dll in Windows, or binary or packaged in Python GUI frameworks like Kivy.
Don’t use this to gain unwanted access to any computer without permission because it is illegal. Do not use this program for any illegal reasons even though it’s in its simplest form.






