Software threats have grown at an exponential rate in the last few years. Vulnerabilities in software and applications have caused a lot of damage to different organizations and people. The image below categorizes the severity of vulnerabilities identified in applications:
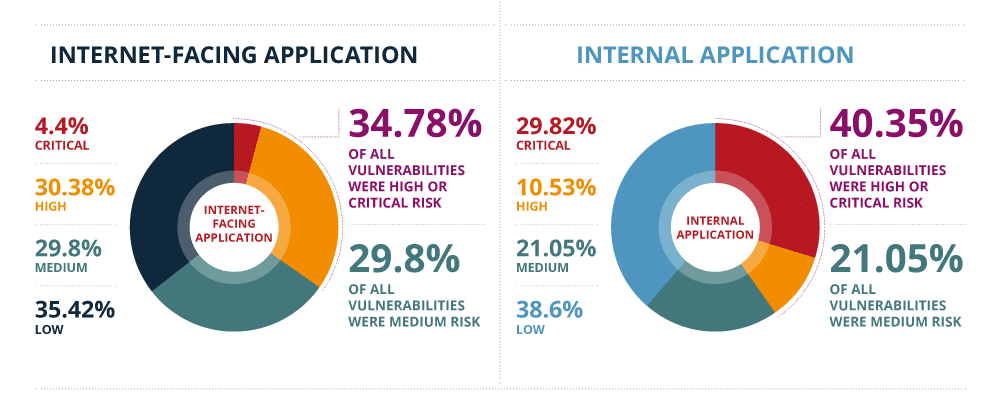
Source: EdgeScan 2020 Vulnerability Statistics Report
Secure coding standards and best practices enable developers to develop applications and software securely. These standards ensure that software developers code their applications securely without leaving any vulnerabilities that may be exploited by different threat actors.
Although there are a number of ways to securely develop applications, OWASP (Open Web Application Security Project) provides a comprehensive secure coding checklist. This secure coding checklist primarily focuses on web applications, but it can be employed as a security protocol for every software development life cycle and software deployment platform to minimize threats associated with bad coding practices.
OWASP provides the following secure coding checklist which has a number of prevention techniques through which damage of different types of software attacks can be minimized and mitigated. We are going to list some of the techniques which come under each of the check list.
Input Validation
Input validation or data validation is a proper check/test administered on input supplied by users or the application. Below is a code snippet that validates input in HTML5 for web browsers:
Source : W3Schools
The input provided checks thoroughly for any parameters that cause the application or software to behave abnormally that can lead to attacks such as injection, buffer overflows and cross site scripting. Some techniques that can be used to perform input validation are:
- Conducting data validation on trusted systems.
- Conduction validation and identification of data in terms of trusted and untrusted sources.
- Validating data based on data type, range and length of input against a list of allowed characters.
- Checking and validating that the values in headers of requests and responses are only in ASCII characters.
- Validating all data provided by the client/user before the data is processed, including URLs, HTTP headers, embedded code etc.
Output Encoding
Output encoding involves translating user input/unsafe data in such a way that when the input is displayed it does not execute as a code in a browser or program. Using this technique, untrusted data in a form that the interpreter does not understand is prevented from being executed.
Cross-site scripting attacks can be avoided using output encoding. Below is an example of what happens in a cross site scripting attack when an aribitary code is added into the input fields and output encoding is not taken care of.
Some of the techniques pointed out by OWASP are:
- Validating data on a trusted system.
- Encoding all characters unless they are deemed safe for the target interpreter.
- Sanitizing untrusted data output using OS commands.
Authentication & Password Management
A user’s identity is recognized using the authentication process. Password management involves a set of rules and techniques that should be followed by users when storing passwords in order to retain confidentiality and availability to certain critical assets/resources. OWASP mentions different techniques for this:
- Require authentication for all resources/pages that link to CIA Triad.
- Prevent the re-using of passwords.
- Notify users when password reset occurs.
- Report the number of login failure to the user upon their next successful login.
- Keep a short expiry time for temporary passwords that needs to be changed upon next login.
- Require passwords to be set on the basis of password complexity policy.
Session Management
The process of securely handling multiple requests from a service of a web application from different users is known as session management.
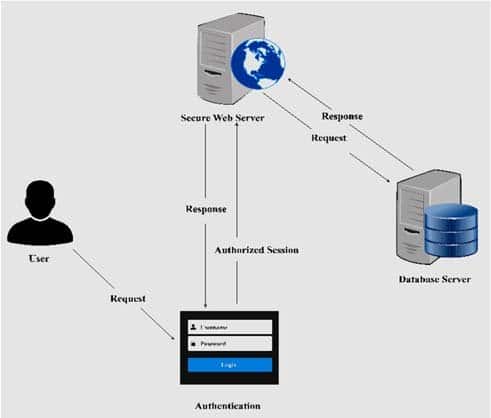
Source: Research Gate
The following are some points on session management from the OWASP checklists:
- Sessions and connections should be fully terminated upon logout.
- Multiple logins should not be allowed against the same User ID.
- Based on the risks and business objectives, session inactivity timeout interval should be as low as possible.
Access Control
Access control is a security technique in which users are given the right to access resources or systems on the basis of their privilege level. Out of a wide range, some techniques of access control are given below:
- Only authorized users should have access to protected URLs, services, application data, user data, attributes etc.
- Account auditing should be implemented and unused accounts should be deleted.
- Accounts associated with different services to external or internal systems that are primarily used for non-critical tasks should be given least privilege.
- The number of transactions should be limited for a single user or device during a particular period of time.
Cryptographic Practices
Cryptographic operations are usually done to encrypt sensitive data so that only intended users can see and make changes to the data, thus maintaining confidentiality. Some of the cryptographic practices are mentioned below:
- A trusted system should be used to implement cryptographic functions to maintain confidentiality of sensitive data on the application.
- The generation of random numbers, file names, GUIDs and strings should use an approved random number generator.
- Cryptographic key management should be employed by developing and using processes and policies.
- Master keys should be protected from unauthorized access.
Error Handling & Logging
Error handling involves procedures that handle unsolicited output, normally experienced when a program or software is supplied with an abnormal input. Logging enables you to keep track of the changes to a software or application. Error handling and logging procedures/techniques are as follows:
- Error handlers that do not throw out debugging information in case of unsolicited input should be used.
- When error conditions occur, memory should be properly freed.
- Logs should not store sensitive information related to systems, sessions etc.
- Logs related to input validation failures, authentication attempts, access control, system exceptions, unexpected changes to data and changes made to security configurations should be maintained and checked thoroughly.
Data Protection
Data protection is the process involving safeguarding of important data from alteration, compromise or loss. The following techniques can be used to protect data in order to maintain confidentiality, integrity and availability:
- Follow the principle of least privilege by limiting user rights and privileges to those systems, information and usability that are required to achieve the required goals and objectives.
- Exclude sensitive data from GET requests found in HTTP.
- Protect server-side code and prevent it from being accessible by the common user. Proper access control should be implemented for critical and sensitive data.
- Autocomplete feature should be excluded while entering data into forms on websites or applications.
Communication Security
All sensitive information is protected by the use of encryption. Transport Layer Security (TLS) can be used for protecting connections in conjunction with different variants of encryption.
- In the case of TLS, failed connections should not downgrade to unsecure protocols.
- For protection of sensitive information over external sources use TLS.
- All connections should be specified with character encoding.
System Configuration
The following checklist should be followed for system configurations:
- Ensure that systems, frameworks and system components are running latest versions and patches.
- Application of least privilege should be on services accounts, webservers and processes.
- HTTP response headers should only include relevant information. OS, webserver version and software frameworks information should not be included.
- Test and development environments should be isolated from production environment.
Database Security
Database security involves security measures that help prevent various threats related to databases.
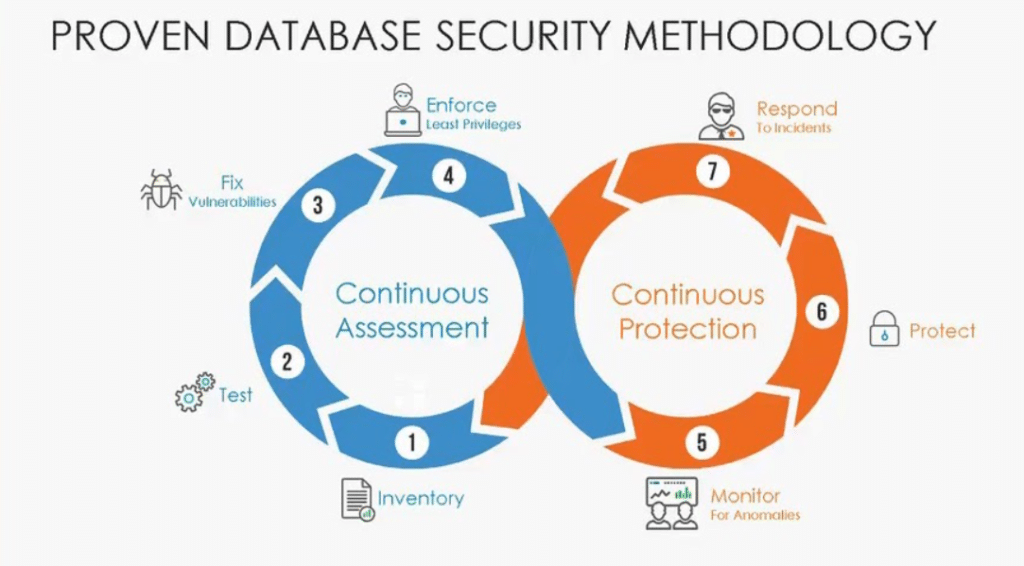
Source : Trustwave
Some of the techniques related to database security are as follows
- While accessing the database, the application should use lowest possible level of privilege.
- Default passwords should be changed immediately. Password hygiene should be kept in mind while assigning passwords to accounts.
- Enable multifactor authentication where applicable. Disable default accounts that are not necessary for business requirements.
File Management
The following are some of the measures and techniques provided by OWASP:
- Ensure authentication while uploading a file on the server.
- Files uploaded on the server should be validated by checking the file headers.
- Execution privileges should be turned off in the directories where files are uploaded.
- Absolute file path should never be sent to the client.
Memory Management
Memory management is a very important aspect when dealing with applications and software as many attacks are related to memory. The following steps could be taken in order to properly manage memory:
- Vulnerable functions such as print, strcat, strcpy etc. should be avoided.
- Buffer size should be checked for overflows.
- Input strings should be truncated properly before functions like copy and concatenation are used.
Conclusion
Incorporating the above-mentioned techniques in your software and web application before it is released in the production environment can surely save you from various attacks that eventually compromises the CIA Triad.





